Malware analysis Malicious activity
4.8
$ 36.00
In stock
(574)
Product Description
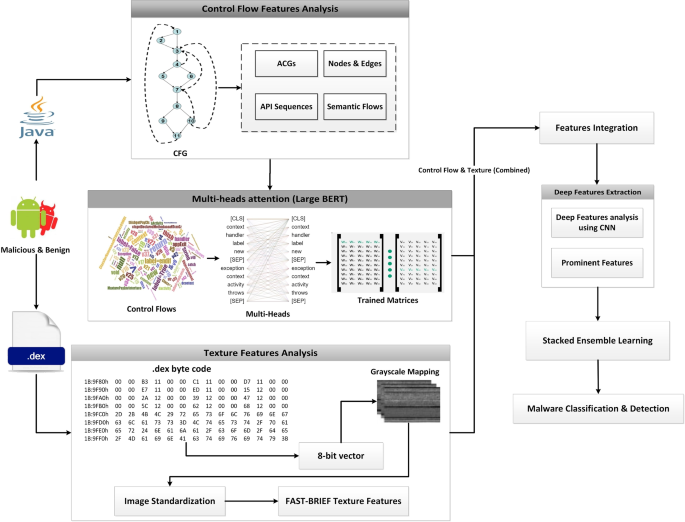
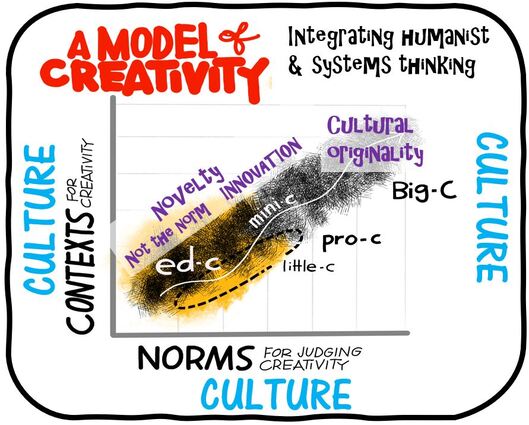
A malware detection system using a hybrid approach of multi-heads attention-based control flow traces and image visualization, Journal of Cloud Computing

A flow chart of malware detection approaches and features.
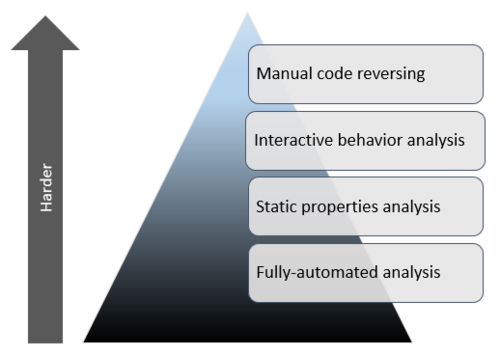
Mastering 4 Stages of Malware Analysis
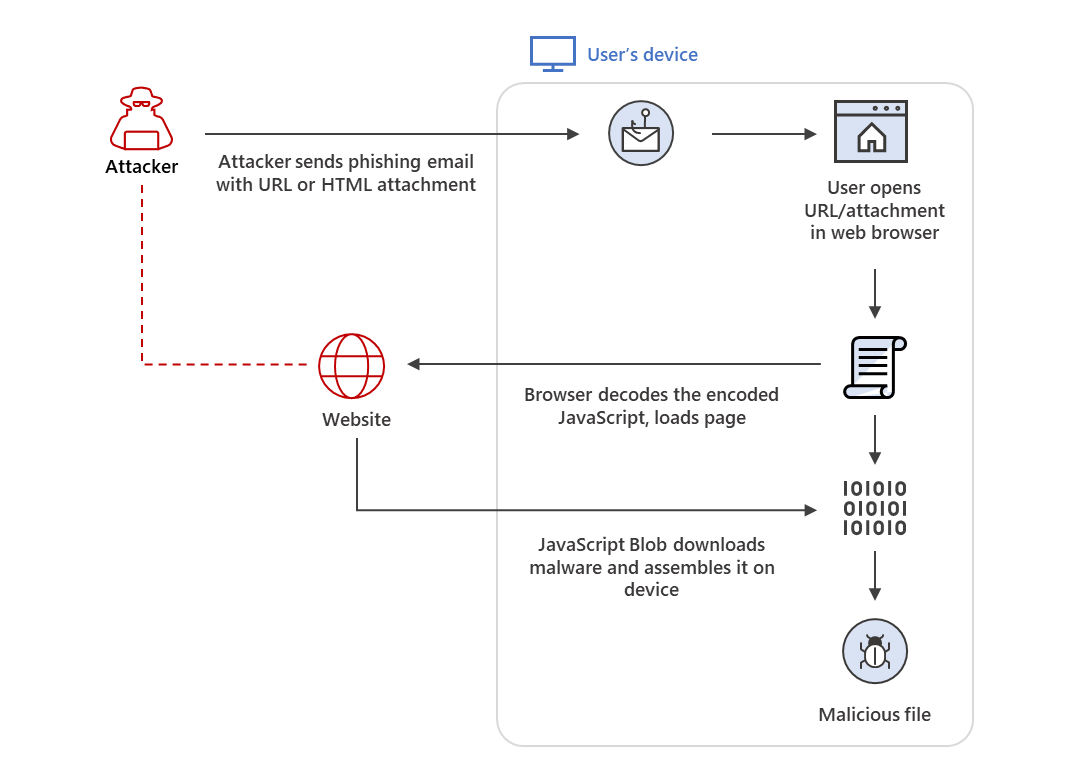
HTML smuggling surges: Highly evasive loader technique increasingly used in banking malware, targeted attacks
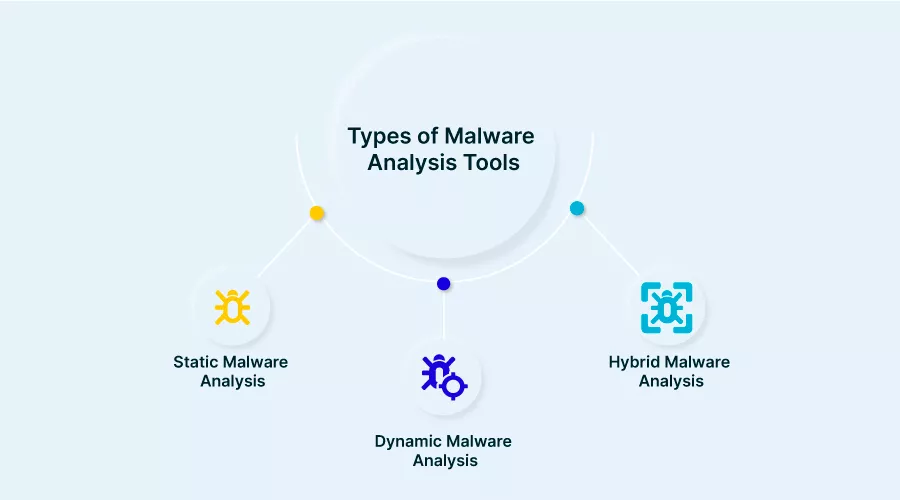
Malware Analysis: Static vs. Dynamic and 4 Critical Best Practices

ChatGPT-powered Malware Analysis
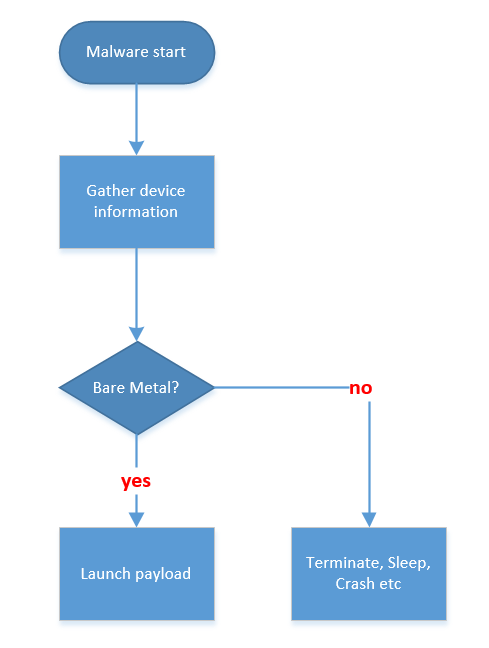
Deep Malware Analysis - Bare Metal - Golden Hardware
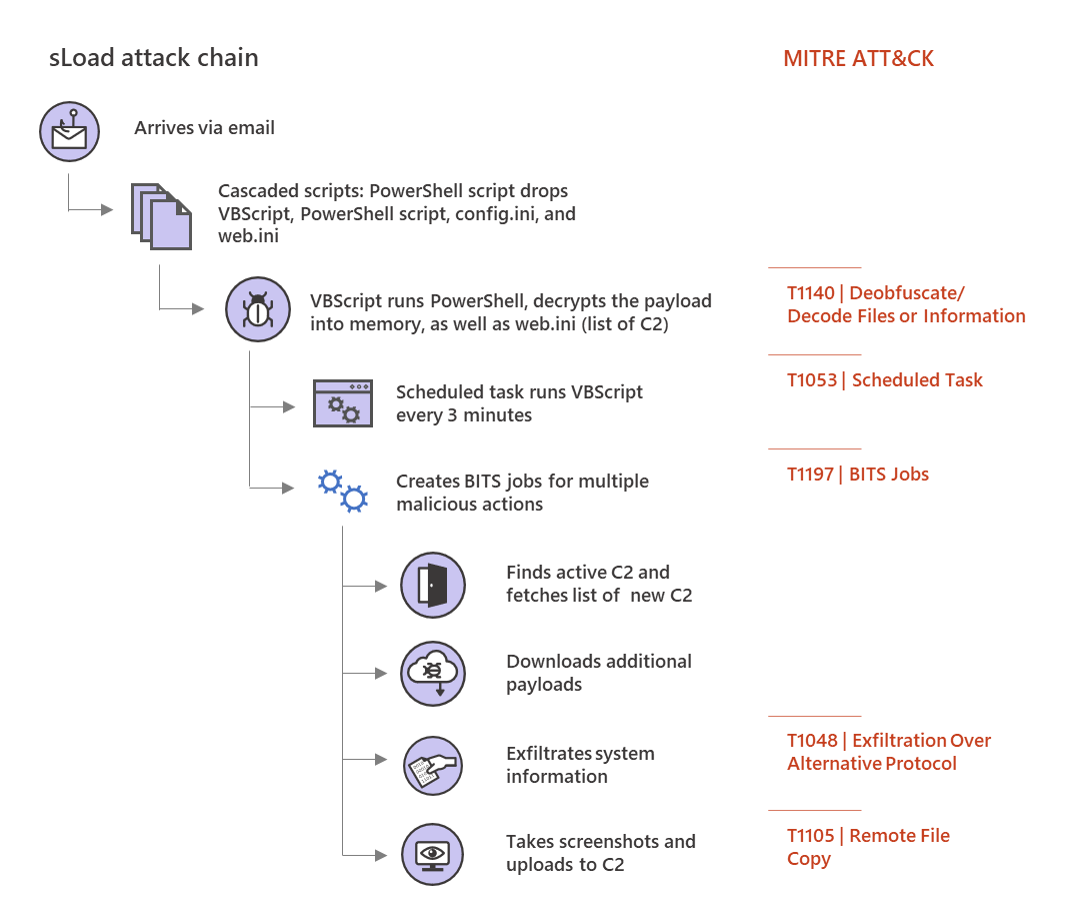
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively for malicious activities
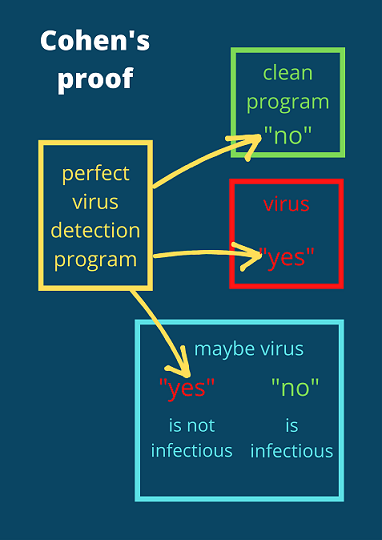
The real reason why malware detection is hard

Dynamic malware analysis flowchart
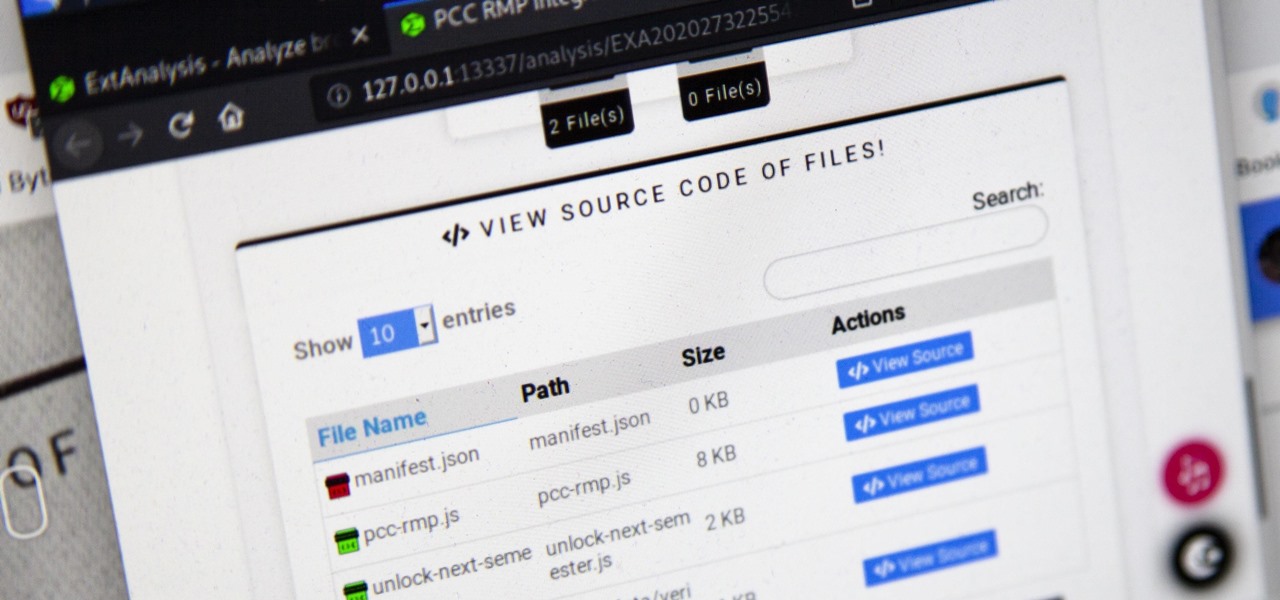
How to Analyze Web Browser Extensions for Possible Malware & Other Malicious Activity « Null Byte :: WonderHowTo




/cloudfront-us-east-1.images.arcpublishing.com/pmn/SKTAQ4XJGVDRPMTNM2R2SY43VQ.jpg)

